Zero Trust Starts with Identity
4:50
Description
Related Videos
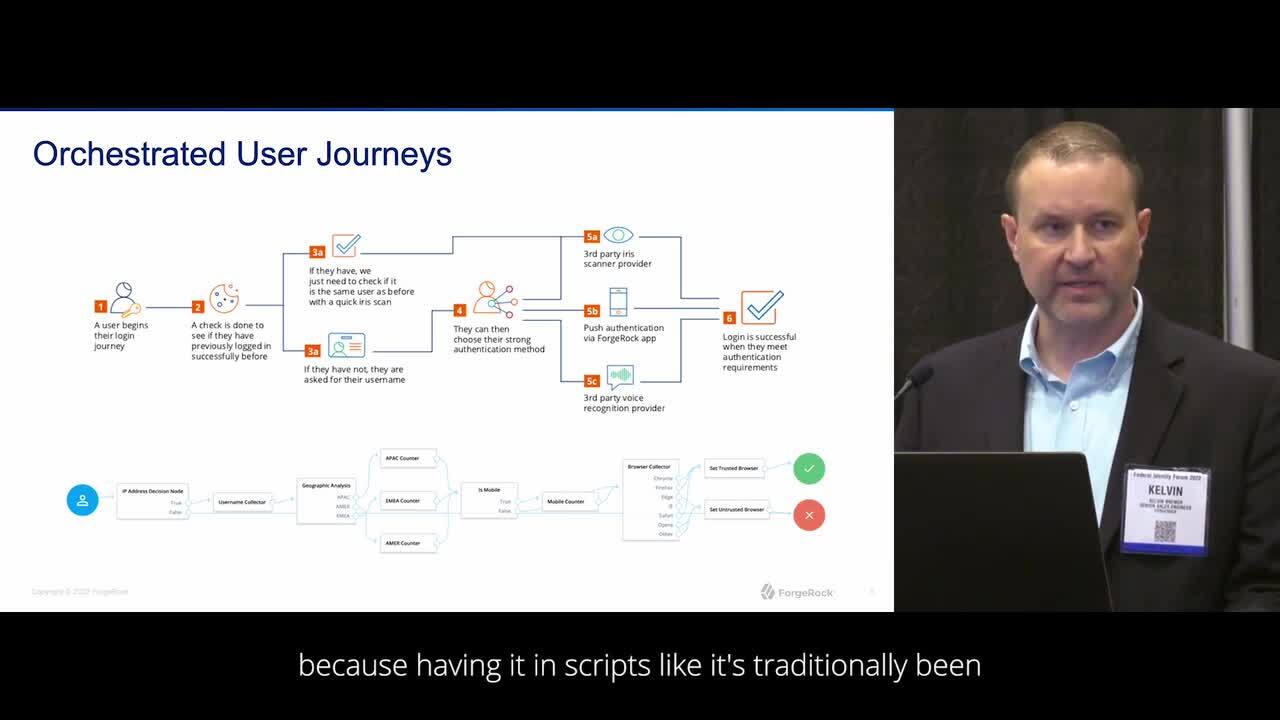
Alex Wawro from Black Hat and Baber Amin, CTO West at Ping Identity discuss the essential components of Zero Trust. Watch the video to discover why identity is key to this approach and the easiest way to get started with a Zero Trust strategy.
View More
View Less