Visualizing PKCE - The Attack
1:41
Description
Related Videos
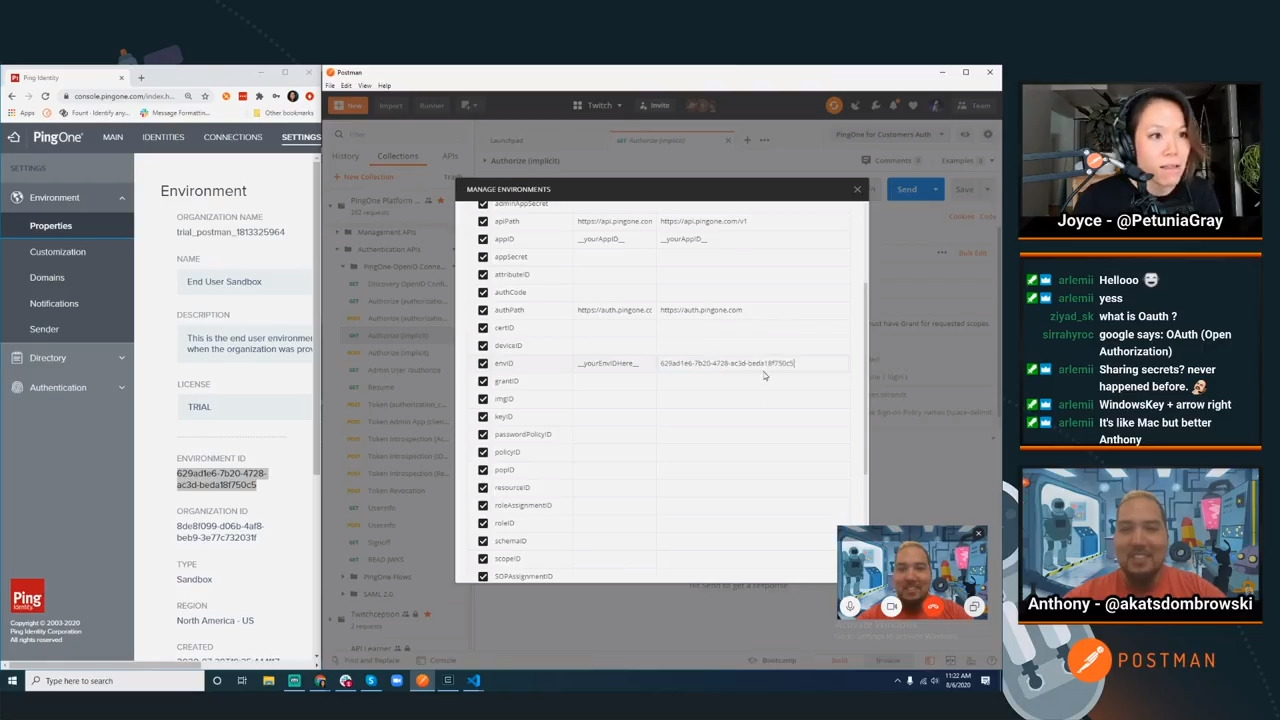
Here's a short scenario to help visualize the attack that sparked the need for PKCE. Gain a deeper understanding of why PKCE is needed by watching this video.
View More
View Less